WASHINGTON, D.C., USA — You’ve seen them… maybe you’ve clicked on them, but hopefully you have ignored them.
I’m talking about “phishing” scams. You know, those very real looking, but fake, emails that claim your car warranty is almost up, or your Netflix account has been compromised?
Now, these scams are coming through in increasing frequency on our cell phones.
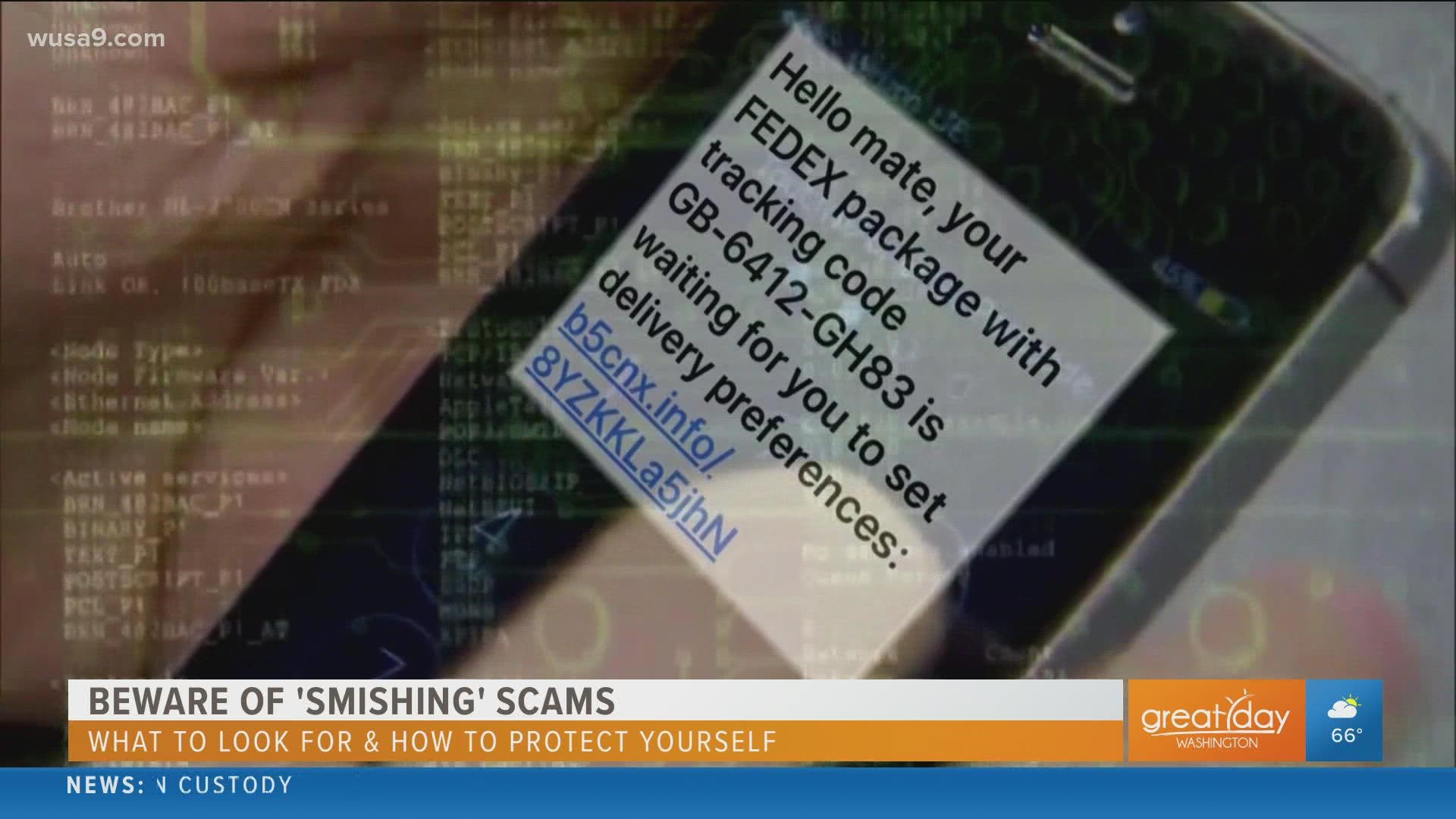
These fraudulent texts, called "smishing" texts (SMS phishing, shortened to “smishing”), try to trick people into sharing personal information that criminals use to steal your identity. So many people are falling for them, and cybercriminals are getting better at executing these cheap, easy and fast cons.
To better understand these popular scans, I talked with Heinan Landa, CEO of Optimal Networks, about how to spot these "smishing" texts and what to do if we receive one.
Let’s start with the basics, what is “smishing”?
"Smishing" is the leading form of malicious text messages, and it can be a personal and business threat as many people bring their devices to work or use them for work.
According to Landa, "smishing" has become so popular because very few emails are responded to any more.
“Gartner reports that that 98% of text messages are read and 45% are responded to. This makes text a very logical place for hackers to attack, especially when Gartner also shows that only 6% of emails are responded to.”
Why is "smishing" so dangerous? How does it work?
Landa says you can fall victim to a "smishing" attack in a couple of ways.
They might trick you to download malware that installs itself on your phone. This malware might masquerade as a legitimate app, tricking you into typing in confidential information and sending this data to the cybercriminals.
On the other hand, the link in the "smishing" message might take you to a fake site where you're asked to type sensitive personal information that the cybercriminals can use to steal your online ID.
Landa says many people are less wary of their phones and many (wrongly) assume their smartphone is better protected than their computer.
He says others just aren’t paying close attention to what they received because they’re using their smartphone on the go.
Who’s at risk? What kind of information are “smishers” looking for?
According to Landa, Android devices remain the prime target for malware—simply because so many of them are out there; and the platform offers greater flexibility for customers (and cybercriminals!)
“Although Apple's iOS mobile technology has a good reputation for security, no mobile operating system can by itself protect you from phishing-style attacks.”
"Smishers" (or "Smishermen") want your personal data which they often then use to steal money/get into personal or company bank accounts.
How can you protect yourself from Smishing?
Landa says be alert!
Take a close look at the message and do not click on any links in messages you receive from unknown numbers.
“These messages tend to show up as urgent security alerts, or 'you must act now' language with coupons, redemptions, offers, deals, etc. These are usually warning signs of a hacking attempt “
On that note, keep an eye out for suspicious numbers that don’t look like real mobile phone numbers. According to Network World, these numbers link to email-to-text services, which are sometimes used by scam artists to avoid providing their actual phone numbers/
Landa reminds us that our banking and financial institutions will not send a text message asking to update account information or confirm codes. Call your bank if you receive a message like this if you are unsure.
Do not store credit card numbers, routing numbers, account numbers, etc. on your smartphone.
Report "smishing" attacks to the Federal Communications Commission (FCC)
What do we do if we fall victim to a "smishing" attack?
Landa says If you believe you have been the victim of a "smishing" attack or other cyber crime, report it to your local law enforcement.
You should also file a complaint with the Internet Crime Complaint Center (IC3) which is managed by the FBI and the Department of Justice, find them online at ic3.gov.
File a report and find more resources on the FTC website identitytheft.gov.
These websites also provide resources to help identify and prevent all sorts of cybercrimes.